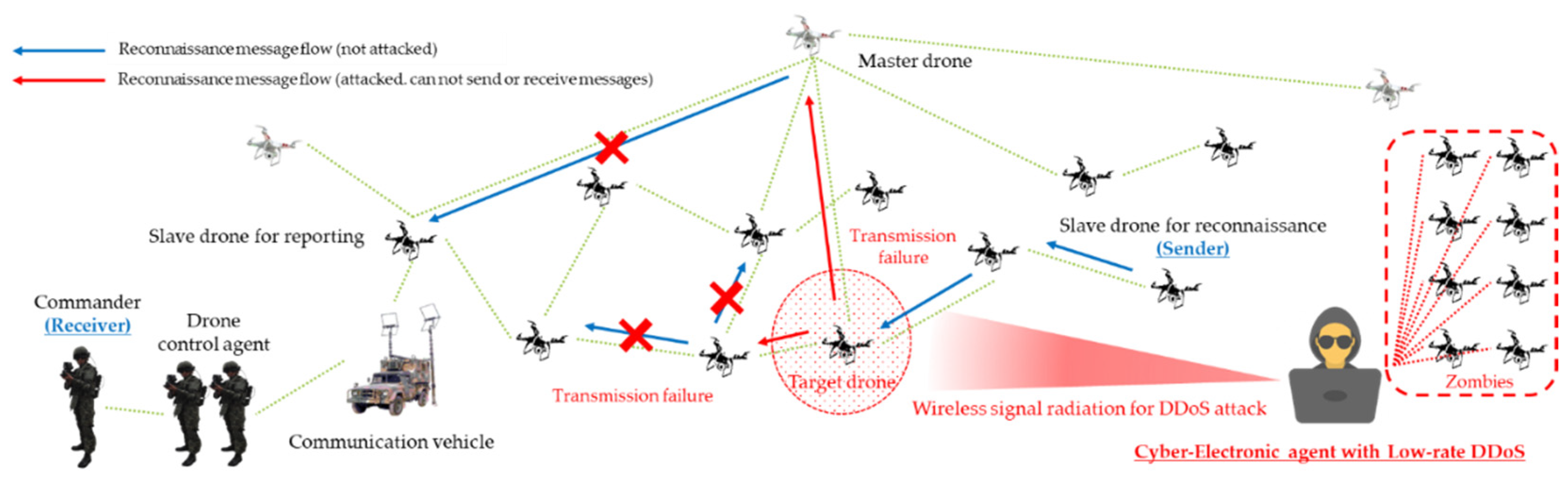
Sensors | Free Full-Text | D-CEWS: DEVS-Based Cyber-Electronic Warfare M&S Framework for Enhanced Communication Effectiveness Analysis in Battlefield | HTML
Securing Against DoS/DDoS Attacks in Internet of Flying Things using Experience-based Deep Learning Algorithm

GitHub suffers from a DDoS attack, Amazon moves drones to Canada, IBM Watson acquires Blekko—SD Times news digest: March 30, 2015 - SD Times
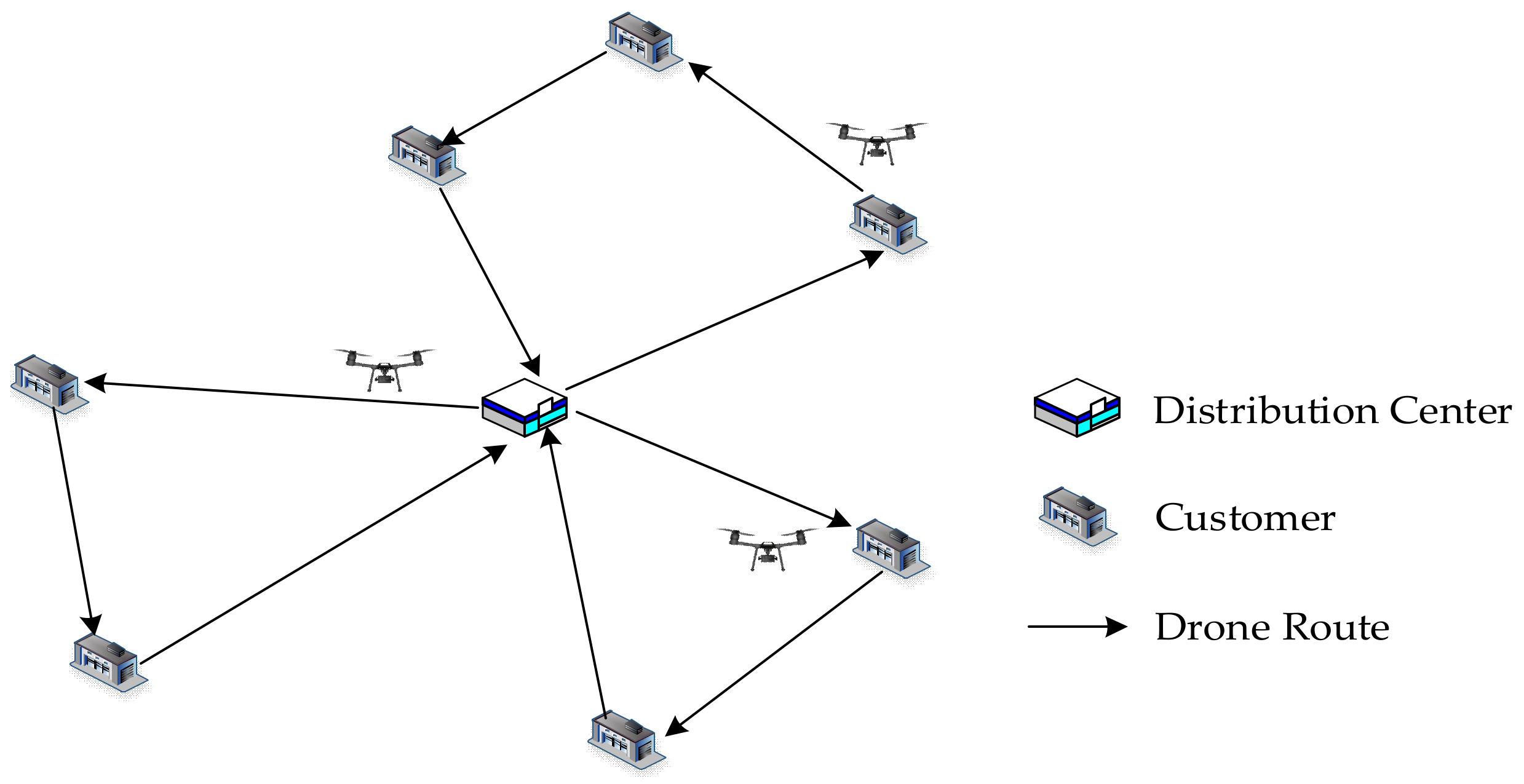
Sustainability | Free Full-Text | Optimal Model and Algorithm of Medical Materials Delivery Drone Routing Problem under Major Public Health Emergencies | HTML
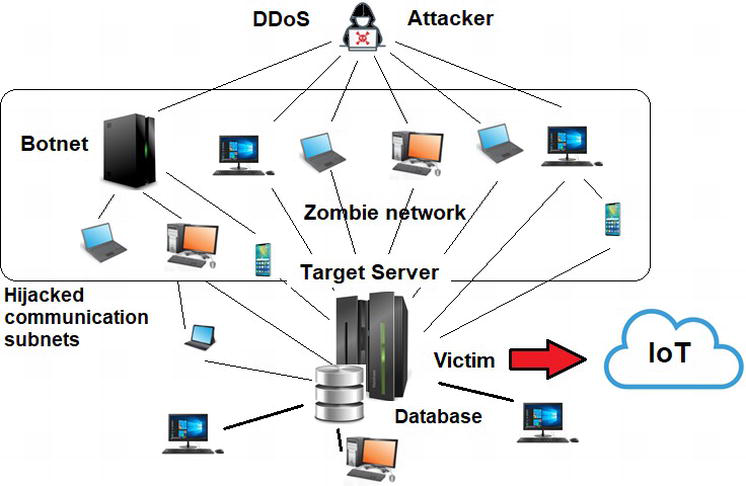
Internet of Things and Distributed Denial of Service as Risk Factors in Information Security | IntechOpen
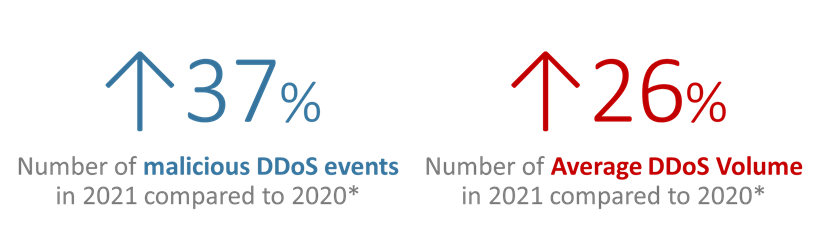
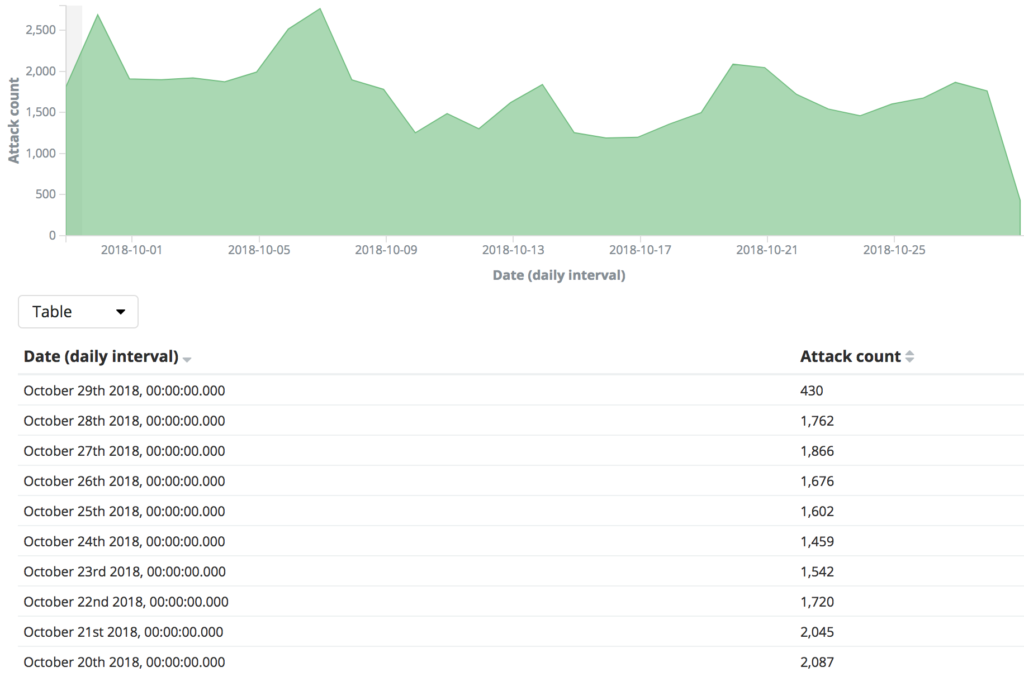
DDoS Protection in the Age of 5G Networks, Edge Computing and Explosive Bandwidth Growth - Security Boulevard
Securing Against DoS/DDoS Attacks in Internet of Flying Things using Experience-based Deep Learning Algorithm

Drone demo shows it's possible to protect 5G-managed devices from DDoS, exfiltration attacks | Network World

Game theoretic solution for an Unmanned Aerial Vehicle network host under DDoS attack - ScienceDirect

Run time variation with increasing number of UAVs for DDoS attack (same... | Download Scientific Diagram

Concerns Security | Distributed Denial of Service Attacks | Moral Issues, Societal Factors Security Although distributed computing looks to provide an efficient means of conducting extraordinarily large scale computations, there are numerous privacy and ...